Trend says hackers have weaponized SpringShell to install Mirai malware

Getty Visuals
Scientists on Friday stated that hackers are exploiting the not long ago discovered SpringShell vulnerability to effectively infect susceptible Net of Things devices with Mirai, an open source piece of malware that wrangles routers and other network-linked gadgets into sprawling botnets.
When SpringShell (also known as Spring4Shell) came to light previous Sunday, some reviews in comparison it to Log4Shell, the significant zero-day vulnerability in the well-liked logging utility Log4J that afflicted a sizable part of apps on the World wide web. That comparison proved to be exaggerated due to the fact the configurations needed for SpringShell to do the job were by no signifies popular. To date, there are no genuine-earth apps recognised to be susceptible.
Researchers at Pattern Micro now say that hackers have produced a weaponized exploit that correctly installs Mirai. A web site article they released didn’t establish the variety of gadget or the CPU used in the contaminated products. The write-up did, nonetheless, say a malware file server they located saved many variants of the malware for various CPU architectures.
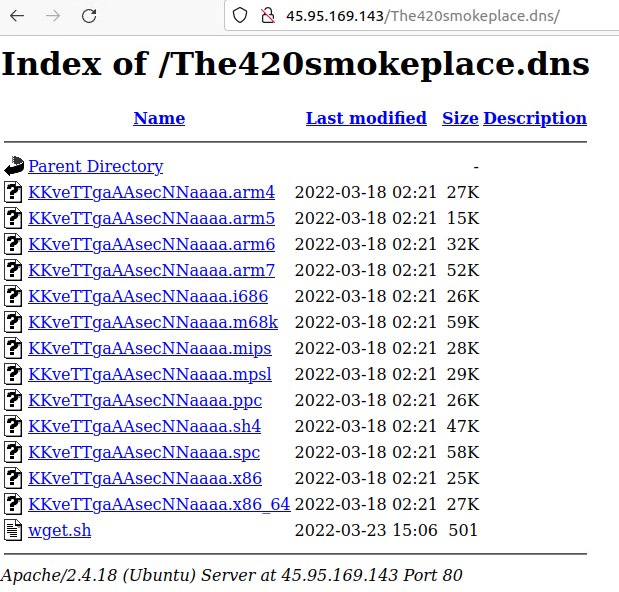
Craze Micro
“We noticed energetic exploitation of Spring4Shell wherein malicious actors have been able to weaponize and execute the Mirai botnet malware on susceptible servers, especially in the Singapore area,” Development Micro scientists Deep Patel, Nitesh Surana, and Ashish Verma wrote. The exploits enable danger actors to obtain Mirai to the “/tmp” folder of the device and execute it adhering to a permission change applying “chmod.”
The assaults commenced appearing in researchers’ honeypots early this month. Most of the vulnerable setups were being configured to these dependencies:
- Spring Framework versions right before 5.2.20, 5.3.18, and Java Growth Kit (JDK) model 9 or higher
- Apache Tomcat
- Spring-webmvc or spring-webflux dependency
- Employing Spring parameter binding that is configured to use a non-simple parameter form, these as Plain Aged Java Objects (POJOs)
- Deployable, packaged as a net software archive (WAR)
Pattern reported the success the hackers experienced in weaponizing the exploit was mainly owing to their ability in using exposed class objects, which offered them many avenues.
“For case in point,” the scientists wrote, “threat actors can access an AccessLogValve object and weaponize the class variable ‘class.module.classLoader.sources.context.parent.pipeline.firstpath’ in Apache Tomcat. They can do this by redirecting the obtain log to write a internet shell into the world wide web root by way of manipulation of the houses of the AccessLogValve object, these types of as its pattern, suffix, directory, and prefix.”
It’s difficult to know specifically what to make of the report. The deficiency of specifics and the geographical tie to Singapore may recommend a constrained variety of devices are vulnerable, or potentially none, if what Development Micro saw was some resource applied by researchers. With no idea what or if true-earth equipment are vulnerable, it’s tricky to give an accurate assessment of the menace or provide actionable tips for avoiding it.
